The red team is a team of external experts who usually carry out real attacks on IT systems at the request of senior management without the knowledge of the IT department. In attacks, “everything is worthwhile” that does not threaten the collapse of the systems.
The terms ‘red team, blue team, purple team’ are often used during security assessments. The red team is the attacking party (the hackers), the blue team is the defending party (the IT department). The purple team is an iteration of these: vulnerabilities usually found by external experts are corrected by internal IT professionals, then the red team attacks again and the blue team defends, and the two teams work together to create a controlled, secure IT environment. This ongoing collaboration is commonly referred to as the purple team.
In a red team assessment, a typical lineup is that those involved in the attack only know about the attack as narrowly as possible, typically the chief executive, the IT security chief, or possibly the head of the IT department. The essence of this secrecy is that the company can assess how well the security policies and systems they have developed meet their expectations.
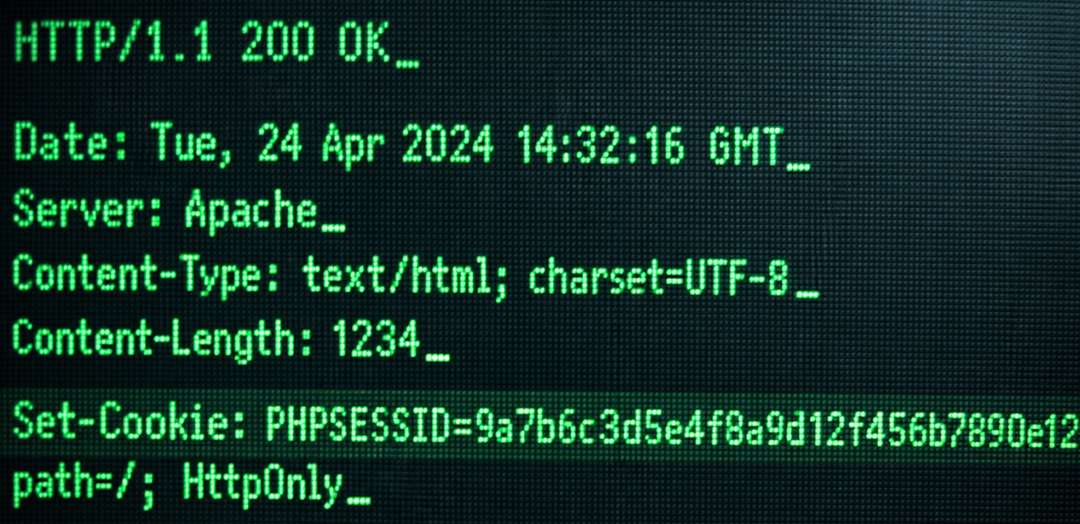
The assessment should be performed from two approaches. First, attackers look for vulnerabilities in their systems based on information found on the Internet. This differs from a vulnerability assessment in that the goal of the red team is to find and successfully exploit a vulnerability, while in a vulnerability assessment, the goal is to find as many errors as possible within the time frame available.
The malicious worker is then usually personified by the red team. Attackers gain low-level access to the internal network (this is often specified in the contract) and then attackers try to access sensitive information. Such information includes passwords, internal databases, that is, any information that, in the hands of the competition (or disclosed), could cause financial damage or loss of prestige to the company.
Whiteshield has been conducting red team assessments against small and large companies and municipal systems for several years. During this period, we gained in-depth knowledge of exploiting the weaknesses of Windows and Linux environments.
Do you have a question? We are happy to answer! Contact us!