HTTP headers and web application security: an underrated layer of defence Discussions around web application security typically focus on backend logic, authentication, WAFs or vulnerability assessments. However, there is a layer that rarely receives attention, despite...
Security insights
Our articles break down how security weaknesses translate into real business risk — and how organizations can address them effectively.
Session fixation explained: Hidden web application security risk
Session fixation: An underestimated threat Session fixation rarely receives the same level of attention as vulnerabilities such as XSS or SQL injection. The reason is simple: it’s less visible, harder to understand, and does not present itself as a classic break-in....
What Does an Ethical Hacker Do? | Business-Focused Guide
What does an ethical hacker do? – And why it is a business question Spoiler: an ethical hacker – aka pentester – is not sitting in a dark basement wearing a black hoodie. Even if Hollywood has done a remarkably good job convincing us otherwise. So what does an ethical...
Clickjacking attack explained: Transparent layers, iFrames and user manipulation
Clickjacking: When a click doesn’t mean what you think In the world of web security, many attacks rely on complex exploits, vulnerable code or poorly configured systems, but clickjacking belongs to a very different category. Here, the attacker’s goal is not to break...
What makes a good password? Password policy explained | Ethical hacker insight
Password policy explained: What makes a good password? Passwords remain the most widely used authentication mechanism in the digital world. That’s why the “good password” is kinda treated as the Holy Grail. Banking applications, enterprise systems, cloud platforms,...
Case study: The hacker and the one-cent hotel room
A 20-year-old hacker identified a security flaw in the online booking systems of Spanish luxury hotels and managed to reserve rooms and premium apartments for just 1 cent each. The largest single loss exceeded €4,000, while the cumulative damage reportedly reached...
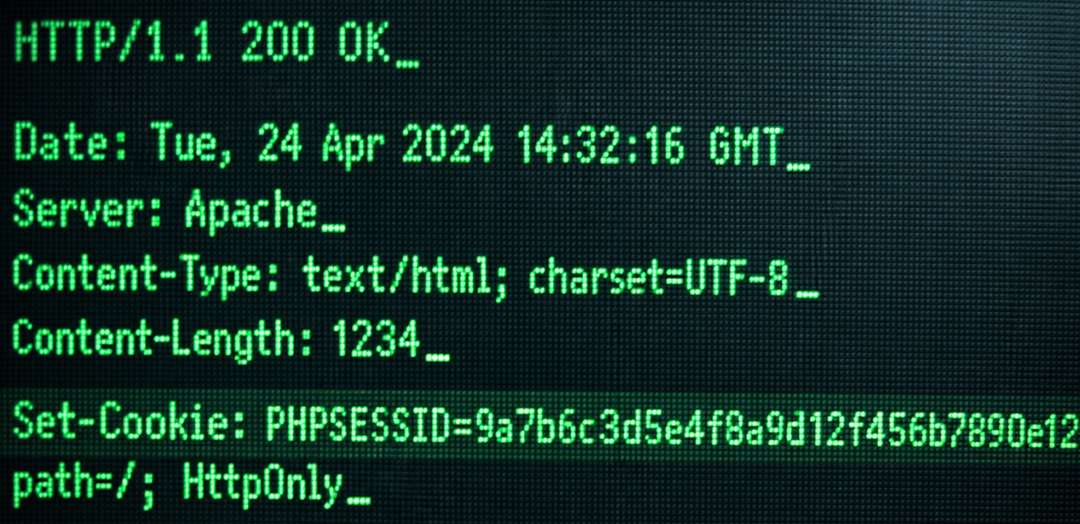
Cookie attributes: The small configuration choices that define web security
A poorly configured cookie is often the quiet enabler behind session hijacking, account takeover and cross-site attacks. Not because cookies are inherently insecure, but because their security controls are left at default settings. XSS protection and CSRF mitigation...
Port scanning for CISOs | Exposure management & attack surface visibility
Port scanning: Why should you knock on every door? You may think port scanning requires no more expertise than reading a water meter. Port scanning is regularly the foundation of internet hygiene, so it definitely does. Port scanning is checking whether you locked the...
Security Starts With a Conversation
Skip the sales pitch. Have a high-level conversation about your business
continuity and operational risk.