HTTP headers and web application security: an underrated layer of defence
Discussions around web application security typically focus on backend logic, authentication, WAFs or vulnerability assessments. However, there is a layer that rarely receives attention, despite having a direct impact on how browsers handle server responses. This layer is the HTTP header configuration.
It is true that properly configured HTTP security headers are not particularly visible controls. They do not fix SQL injection vulnerabilities, nor do they prevent logical flaws. However, with minimal implementation effort, they can significantly reduce the success rate of client-side attacks – which is precisely why they should not be overlooked.
What is an HTTP header, and why does it matter for a web application?
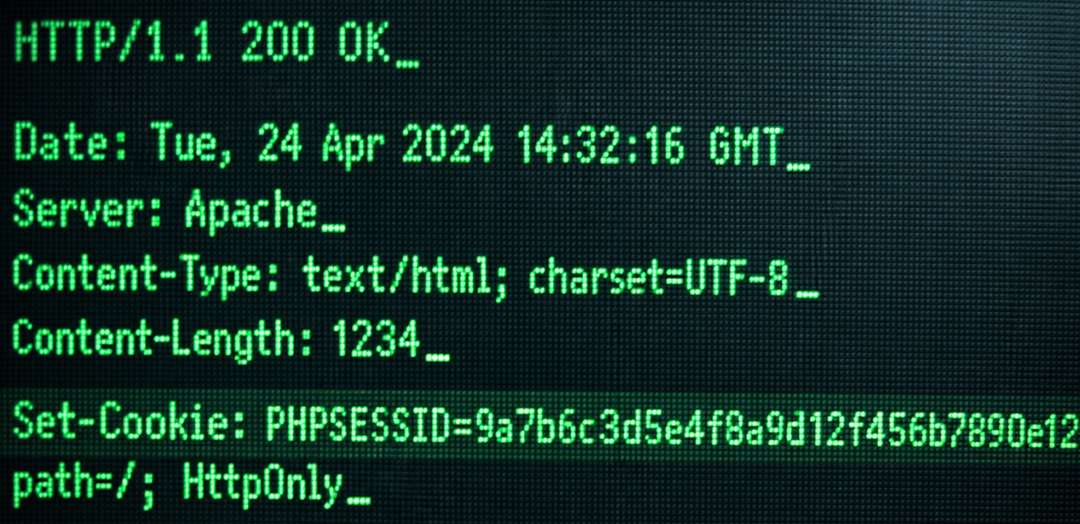
During HTTP communication, the client (typically a browser) and the server exchange structured messages. These consist of two main parts: headers (metadata) and the body (the actual content).
An HTTP header is a key–value pair that defines how the response should be interpreted or handled. It indicates, for example, the content type, caching behaviour and which security rules should be applied during processing.
Security headers go a step further: they enforce explicit behavioural rules on the browser. This does not mean that HTTP becomes an additional security solution, but rather that the protocol’s native capabilities are used more deliberately to strengthen a web application’s security posture.
Cyber hygiene: low cost, high impact
HTTP security headers fall into the category of cyber hygiene controls. They do not require complex development work and are typically configured at the infrastructure level, yet they measurably reduce the attack surface.
In practice, almost all modern web servers, reverse proxies, and frameworks support their configuration. If they are not present, this is rarely due to technical limitations – it is far more often a matter of prioritisation or awareness.
What types of attacks can HTTP headers mitigate?
Properly configured HTTP headers do not prevent a single specific attack, but rather reduce the impact of multiple attack vectors, including:
- SSL stripping and protocol downgrade attacks (weakening encrypted communication)
- Cross-Site Scripting (XSS), involving malicious script execution in the browser
- Clickjacking, where users are manipulated via hidden interface elements
- MIME sniffing-based attacks (misinterpreting content types)
- Data leakage via referrer information
- Unnecessary access to browser APIs (camera, microphone, etc.)
- Cross-origin data access issues
It is important to emphasise that these headers are not patches. They do not eliminate vulnerabilities, but they can significantly limit how those vulnerabilities can be exploited.
The most important HTTP security headers
During penetration testing, we consistently observe that even in otherwise mature web application environments, header configurations are either missing or inconsistent. Staging and production often differ, and configurations between reverse proxies and application layers frequently diverge.
This is problematic because browsers do not make decisions based on context, but on the responses they receive. If policies are not clearly and consistently defined, the client-side attack surface remains effectively exposed – regardless of how strong the backend may be.
Below are the headers most commonly associated with real-world attack scenarios when absent or misconfigured.
Strict-Transport-Security (HSTS)
Example: Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
HSTS instructs the browser to communicate exclusively over HTTPS with a given domain.
What does this mean in practice?
The browser remembers that HTTP must not be used. All connections are automatically upgraded to HTTPS, and the domain can even be included in browser preload lists.
What does it mitigate?
Primarily, SSL stripping attacks. In such cases, an attacker attempts to downgrade a user’s connection from HTTPS to HTTP to intercept unencrypted traffic. HSTS prevents this entirely by disallowing such downgrades.
Content-Security-Policy (CSP)
Example: Content-Security-Policy: default-src ‘self’; object-src ‘none’; frame-ancestors ‘none’;
CSP is one of the most powerful client-side controls. It declaratively defines where the browser is allowed to load resources, including JavaScript, CSS, images, iframes, and API calls.
What does it do?
It restricts resource loading to the same origin, blocks plugin-based objects and prevents embedding via iframes.
What does it mitigate?
Primarily, the impact of XSS attacks. It does not necessarily eliminate the vulnerability, but it significantly constrains the attacker’s ability to execute malicious code.
It is worth noting that CSP requires careful tuning: too strict → broken functionality. Too permissive → minimal protection.
X-Content-Type-Options
Example: X-Content-Type-Options: nosniff
This header prevents the browser from guessing the content type of a resource.
Why is this important?
In MIME sniffing scenarios, the browser may override the declared Content-Type and interpret content as executable code. The nosniff directive prevents this behaviour.
It is typically a low-effort control with minimal side effects, making it a quick security improvement.
X-Frame-Options
Example: X-Frame-Options: DENY or X-Frame-Options: SAMEORIGIN
This header controls whether a page can be embedded within an iframe.
What does it mitigate?
It helps defend against clickjacking attacks, in which a legitimate page is embedded within a malicious interface, tricking users into performing unintended actions, such as approving a transaction.
Note: modern approaches often rely on the CSP frame-ancestors directive for more granular control. However, X-Frame-Options remains a simple and effective baseline defence.
Missing or misconfigured HTTP security headers represent a systemic risk
During penetration testing, a consistent pattern emerges: HTTP security headers are either entirely absent or present but offer no meaningful protection. Default configurations are frequently deployed in production, and CSP is often implemented in a way that effectively allows everything – creating a false sense of security rather than real control.
The issue is not technical complexity. These configurations do not require months of development or architectural redesign.
However, while organisations are deciding who is responsible, when implementation should happen, and whether it is a priority at all, vulnerabilities remain exploitable.
What is particularly noteworthy is that these gaps often occur in environments where significant security investment has already been made. There may be a WAF, MFA and regular audits in place – yet browser behaviour remains effectively uncontrolled.
HTTP headers as a baseline requirement
HTTP security headers do not replace secure development practices, code quality or regular vulnerability assessments. However, they introduce a control layer that directly influences client-side behaviour.
When properly configured, they reduce the attack surface, limit the impact of successful exploits and make common web attack techniques significantly more difficult to execute.
Their implementation typically requires minimal effort and can be handled at the infrastructure or configuration level, making them quick to deploy. For this reason, they should not be considered advanced security features, but baseline requirements.
Their absence may not immediately lead to compromise, but it lowers the barrier for attackers – and they are well aware of this.
Because from an attacker’s perspective, the question is simple: why look for complex exploits if client-side controls are not enforced in the first place?
When was the last time you reviewed your web application’s HTTP header configuration? If you are confident it is consistent across all environments, there may be nothing to do. If not, it may be worth taking a closer look. Contact us!