Password policy explained: What makes a good password?
Passwords remain the most widely used authentication mechanism in the digital world. That’s why the “good password” is kinda treated as the Holy Grail. Banking applications, enterprise systems, cloud platforms, and social media accounts all rely on a sequence of characters to determine whether someone should be granted access.
But what actually makes a good password? From an ethical hacker’s perspective, the answer is not as simple as “make it complex.”
A good password is defined differently depending on whether we are looking at the problem from the perspective of an individual user or an organisation responsible for protecting critical systems. Understanding this difference is essential for building effective password policies and reducing real-world cybersecurity risks.
Why a good password still matters
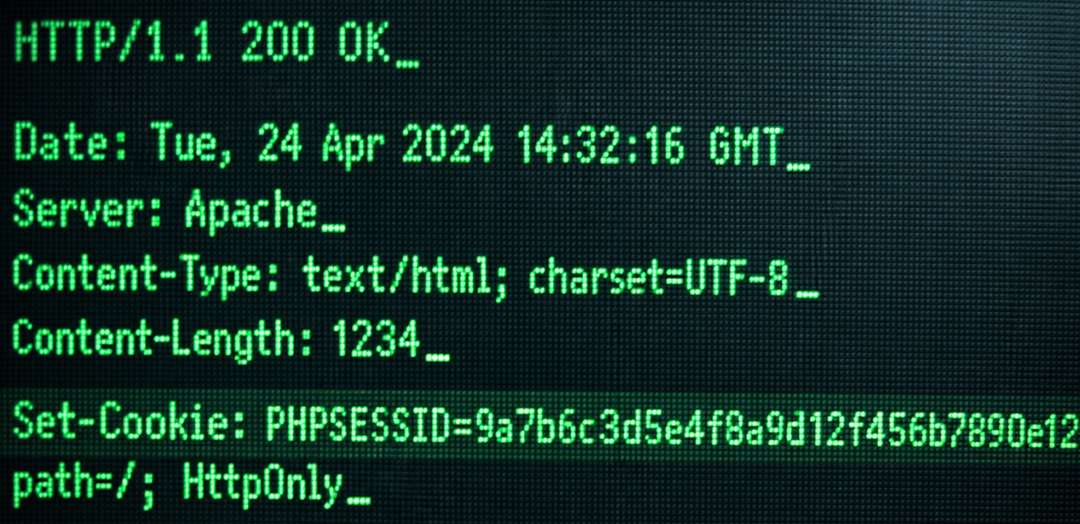
Despite the rise of biometric authentication and multi-factor authentication (MFA), passwords remain the first line of defence in most systems. At the same time, attackers’ capabilities have increased dramatically.
Today, GPU-based password cracking tools can test billions of password guesses per second. Cloud infrastructure enables attackers to rent computing power at relatively low cost, making large-scale password attacks highly accessible.
Consider a simple example! An 8-character password containing only lowercase letters provides 26⁸ possible combinations. That’s roughly 208 billion possibilities.
While this may sound secure, modern cracking tools can test such combinations extremely quickly. In many cases, the entire space can be exhausted within hours or even minutes, especially if the attacker already has access to password hash databases from previous data breaches.
From a technical standpoint, two factors determine whether a password is strong: length and character set diversity. If an 8-character password only contains lowercase letters, the search space is limited to 26⁸ combinations. However, if the password includes uppercase letters, numbers, and special characters, the character pool expands to roughly 94 possible characters, producing 94⁸ combinations.
The real improvement comes from increasing password length. A 12-character password with a mix of characters increases cracking time dramatically. When truly random, such passwords may take extremely long to break using conventional brute-force methods. (Even if ethical hackers rarely rely solely on brute force.)
In real penetration tests, attackers combine several techniques:
- dictionary attacks;
- pattern-based guessing;
- password spraying;
- credential stuffing using leaked password databases.
In practice, many passwords fall long before the theoretical maximum cracking time is reached.
Common password patterns attackers exploit
One of the most common misconceptions is that small modifications automatically turn a weak password into a good password. (e.g.: password → Password1!)
From a user’s perspective, this appears stronger. From an attacker’s perspective, it is one of the first combinations tested. Be aware that password cracking tools are designed to exploit common behavioural patterns such as:
- capitalising the first letter;
- adding “1”, “123”, or “!” at the end;
- inserting years or months (e.g. Password2024!);
- repeating characters such as aaaa1111.
These patterns drastically reduce effective password strength because they are included in automated cracking rule sets, making them low-hanging fruit during security assessments.
The practical definition of a good password for users
For individual users, the most effective approach is often a long passphrase rather than a short complex password. Instead of focusing only on complexity, passphrases prioritise length and memorability. (For example: BlueLamp-Moon92-Silence)
Such passphrases combine unrelated words and create longer authentication strings that are significantly harder to guess or brute-force. In practice, length contributes more to password strength than complexity alone. This approach also reduces the temptation to write passwords down or reuse them across multiple platforms.
Password policy from an enterprise security perspective
For organisations, password security is not only an individual responsibility; it is a system-wide risk management issue, as a single compromised password can lead to lateral movement within a corporate network, privilege escalation, and large-scale data breaches.
For this reason, banks and large enterprises enforce strict password policies. Typical elements of a corporate password policy include:
- minimum password length requirements (often 12–16 characters);
- complexity requirements (uppercase, lowercase, numbers, special characters);
- restrictions on password reuse;
- mandatory password rotation (e.g. every 90 days);
- account lockout mechanisms after multiple failed login attempts.
The logic behind periodic password changes is straightforward: if a password becomes compromised, its usable lifetime should remain limited.
Some systems also prevent users from selecting passwords that contain elements of the previous password, preventing simple variations such as Password04! to Password05! However, modern cybersecurity recommendations have become more nuanced.
Frequent forced password changes can unintentionally encourage users to adopt predictable modification patterns, weakening overall security. As a result, many organisations now combine password policies with multi-factor authentication (MFA), significantly improving protection against account compromise.
Security is not only about the password
Needless to say, human behaviour often represents the weakest link in security, because even the strongest password loses its value if users handle it carelessly.
Passwords written on sticky notes, screenshots containing login credentials or password reuse across personal and corporate services are the most common ways for attackers to break in.
In a real-world attack scenario, gaining access to a single reused password can provide entry into multiple systems. This is why effective security must combine technical controls, user awareness, and organisational policy.
The real meaning of a good password
From a user’s perspective, a good password is long, unique and memorable.
From an enterprise perspective, a good password is part of a structured password policy supported by monitoring, authentication controls, and security awareness.
Ultimately, cybersecurity does not depend on a single string of characters. True resilience comes from the combination of strong authentication practices, effective password policy, and informed user behaviour.